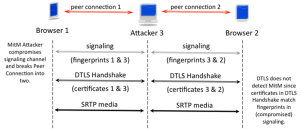
WebRTC is supposed to be secure. A lot more than previous VoIP standards. It isn’t because it uses any special new mechanism, but rather because it takes it seriously and mandates it for all sessions. Alan Johnston decided to take WebRTC for a MitM spin – checking how easy is it to devise a man-in-the-middle […]